- Log in to:
- Community
- DigitalOcean
- Sign up for:
- Community
- DigitalOcean
By Elliot Cooper and Kathryn Hancox
Not using Debian 10?
Choose a different version or distribution.
The author selected the Open Internet/Free Speech Fund to receive a donation as part of the Write for DOnations program.
Introduction
Jitsi Meet is an open-source video-conferencing application based on WebRTC. A Jitsi Meet server provides multi-person video conference rooms that you can access using nothing more than your browser and provides comparable functionality to a Zoom or Skype conference call. The benefit of a Jitsi conference is that all your data only passes through your server, and the end-to-end TLS encryption ensures that no one can snoop on the call. With Jitsi you can be sure that your private information stays that way.
In this tutorial, you will install and configure a Jitsi Meet server on Debian 10. The default configuration allows anyone to create a new conference room. This is not ideal for a server that is publicly available on the internet so you will also configure Jitsi Meet so that only registered users can create new conference rooms. After you have created the conference room, any users can join, as long as they have the unique address and the optional password.
Prerequisites
Before you begin this guide you’ll need the following:
- One Debian 10 server set up by following the Initial Server Setup with Debian 10 tutorial, including a non-root sudo-enabled user. The size of the server you will need mostly depends on the available bandwidth and the number of participants you expect to be using the server. The following table will give you some idea of what is needed.
- A domain name configured to point to your server. You can learn how to point domains to DigitalOcean Droplets by referring to the Domains and DNS guide. Throughout this guide, the example domain name
jitsi.your-domainis used.
When you are choosing a server to run your Jitsi Meet instance you will need to consider the system resources needed to host conference rooms. The following benchmark information was collected from a single-core virtual machine using high-quality video settings:
| CPU | Server Bandwidth | |
|---|---|---|
| Two Participants | 3% | 30Kbps Up, 100Kbps Down |
| Three Participants | 15% | 7Mbps Up, 6.5Mbps Down |
The jump in resource use between two and three participants is because Jitsi will route the call data directly between the clients when there are two of them. When more than two clients are present then call data is routed through the Jitsi Meet server.
Step 1 — Setting the System Hostname
In this step, you will change the system’s hostname to match the domain name that you intend to use for your Jitsi Meet instance and resolve that hostname to the localhost IP, 127.0.0.1. Jitsi Meet uses both of these settings when it installs and generates its configuration files.
First, set the system’s hostname to the domain name that you will use for your Jitsi instance. The following command will set the current hostname and modify the /etc/hostname that holds the system’s hostname between reboots:
- sudo hostnamectl set-hostname jitsi.your-domain
The command that you ran breaks down as follows:
hostnamectlis a utility from the systemd tool suite to manage the system hostname.set-hostnamesets the system hostname.
Check that this was successful by running the following:
- hostname
This will return the hostname you set with the hostnamectl command:
Outputjitsi.your-domain
Next, you will set a local mapping of the server’s hostname to the loopback IP address, 127.0.0.1. Do this by opening the /etc/hosts file with a text editor:
- sudo nano /etc/hosts
Then, add the following line:
127.0.0.1 jitsi.your-domain
Mapping your Jitsi Meet server’s domain name to 127.0.0.1 allows your Jitsi Meet server to use several networked processes that accept local connections from each other on the 127.0.0.1 IP address. These connections are authenticated and encrypted with a TLS certificate, which is registered to your domain name. Locally mapping the domain name to 127.0.0.1 makes it possible to use the TLS certificate for these local network connections.
Save and exit your file.
Your server now has the hostname that Jitsi requires for installation. In the next step, you will open the firewall ports that are needed by Jitsi and the TLS certificate installer.
Step 2 — Configuring the Firewall
When you followed the Initial Server Setup with Debian 10 guide you enabled the UFW firewall and opened the SSH port. The Jitsi server needs some ports opened so that it can communicate with the call clients. Also, the TLS installation process needs to have a port open so that it can authenticate the certificate request.
The ports that you will open are the following:
80/tcpused in the TLS certificate request.443/tcpused for the conference room creation web page.4443/tcp,10000/udpused to transmit and receive the encrypted call traffic.
Run the following ufw commands to open these ports:
- sudo ufw allow 80/tcp
- sudo ufw allow 443/tcp
- sudo ufw allow 4443/tcp
- sudo ufw allow 10000/udp
Check that they were all added with the ufw status command:
- sudo ufw status
You will see the following output if these ports are open:
OutputStatus: active
To Action From
-- ------ ----
OpenSSH ALLOW Anywhere
80/tcp ALLOW Anywhere
443/tcp ALLOW Anywhere
4443/tcp ALLOW Anywhere
10000/udp ALLOW Anywhere
OpenSSH (v6) ALLOW Anywhere (v6)
80/tcp (v6) ALLOW Anywhere (v6)
443/tcp (v6) ALLOW Anywhere (v6)
4443/tcp (v6) ALLOW Anywhere (v6)
10000/udp (v6) ALLOW Anywhere (v6)
The server is now ready for the Jitsi installation, which you will complete in the next step.
Step 3 — Installing Jitsi Meet
In this step, you will add the Jitsi stable repository to your server and then install the Jitsi Meet package from that repository. This will ensure that you are always running the latest stable Jitsi Meet package.
First, install the gnupg package that enables the system to manage GPG cryptographic keys:
- sudo apt install gnupg
Next, download the Jitsi GPG key with the wget downloading utility:
- wget https://download.jitsi.org/jitsi-key.gpg.key
The apt package manager will use this GPG key to validate the packages that you will download from the Jitsi repository.
Now, add the GPG key you downloaded to apt’s keyring using the apt-key utility:
- sudo apt-key add jitsi-key.gpg.key
You can now delete the GPG key file as it is no longer needed:
- rm jitsi-key.gpg.key
Now, you will add the Jitsi repository to your server by creating a new source file that contains the Jitsi repository. Open and create the new file with your editor:
- sudo nano /etc/apt/sources.list.d/jitsi-stable.list
Add this line to the file for the Jitsi repository:
deb https://download.jitsi.org stable/
Save and exit your editor.
Finally, perform a system update to collect the package list from the Jitsi repository and then install the jitsi-meet package:
- sudo apt update
- sudo apt install jitsi-meet
During the installation of jitsi-meet you will be prompted to enter the domain name (for example, jitsi.your-domain) that you want to use for your Jitsi Meet instance.
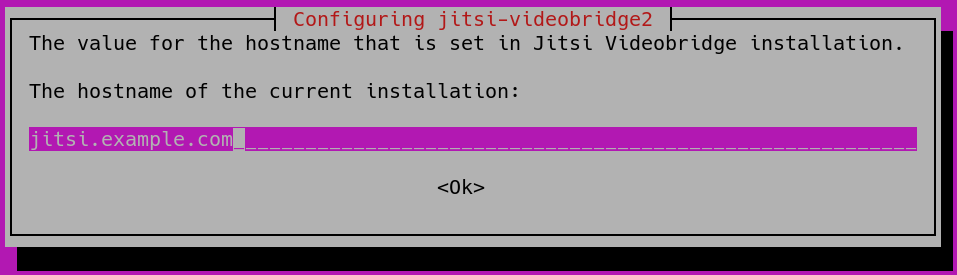
Note: You move the cursor from the hostname field to highlight the <OK> button with the TAB key. Press ENTER when <OK> is highlighted to submit the hostname.
You will then be shown a new dialog box that asks if you want Jitsi to create and use a self-signed TLS certificate or use an existing one you already have:
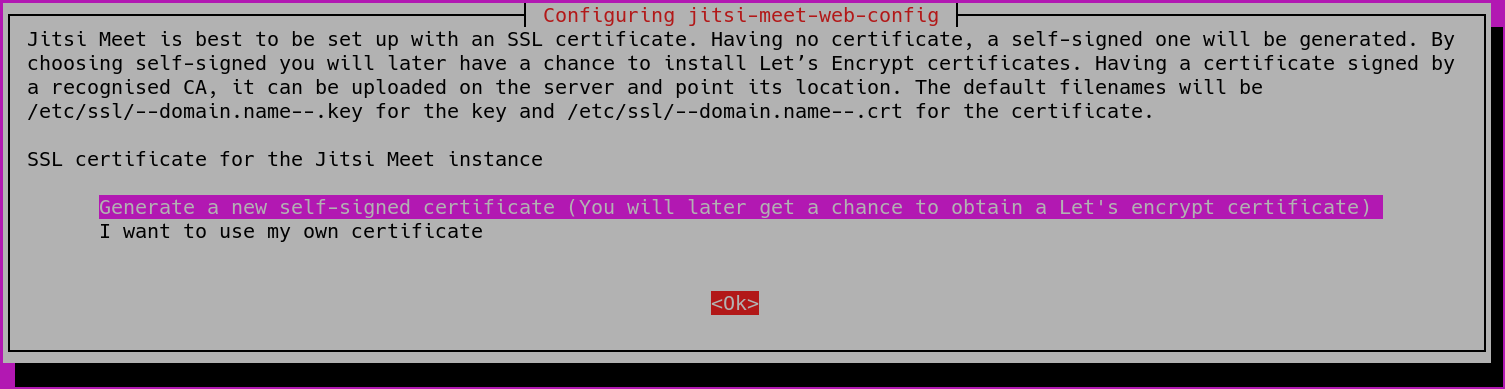
If you do not have a TLS certificate for your Jitsi domain select the first, Generate a new self-signed certificate, option.
Your Jitsi Meet instance is now installed using a self-signed TLS certificate. This will cause browser warnings, so you will get a signed TLS certificate in the next step.
Step 4 — Obtaining a Signed TLS Certificate
Jitsi Meet uses TLS certificates to encrypt the call traffic so that no one can listen to your call as it travels over the internet. TLS certificates are the same certificates that are used by websites to enable HTTPS URLs.
Jitsi Meet supplies a program to automatically download a TLS certificate for your domain name that uses the Certbot utility. You will need to install this program before you run the certificate installation script.
First, install the certbot package with the following command:
- sudo apt install certbot
Your server is now ready to run the TLS certificate installation program provided by Jitsi Meet:
- sudo /usr/share/jitsi-meet/scripts/install-letsencrypt-cert.sh
When you run the script you will be shown the following prompt for an email address:
Output-------------------------------------------------------------------------
This script will:
- Need a working DNS record pointing to this machine(for domain jitsi.example.com)
- Download certbot-auto from https://dl.eff.org to /usr/local/sbin
- Install additional dependencies in order to request Let’s Encrypt certificate
- If running with jetty serving web content, will stop Jitsi Videobridge
- Configure and reload nginx or apache2, whichever is used
- Configure the coturn server to use Let's Encrypt certificate and add required deploy hooks
- Add command in weekly cron job to renew certificates regularly
You need to agree to the ACME server's Subscriber Agreement (https://letsencrypt.org/documents/LE-SA-v1.1.1-August-1-2016.pdf)
by providing an email address for important account notifications
Enter your email and press [ENTER]:
This email address will be submitted to the certificate issuer https://letsencrypt.org and will be used to notify you about security and other matters related to the TLS certificate. You must enter an email address here to proceed with the installation. The installation will then complete without any further prompts.
When it finishes, your Jitsi Meet instance will be configured to use a signed TLS certificate for your domain name. Certificate renewals will also happen automatically because the installer placed a renewal script at /etc/cron.weekly/letsencrypt-renew that will run each week.
Your Jitsi Meet server is now up and running and available for testing. Open a browser and point it to your domain name. You will be able to create a new conference room and invite others to join you.
The default configuration for Jitsi Meet is that anyone visiting your Jitsi Meet server homepage can create a new conference room. This will use your server’s system resources to run the conference room and is not desirable for unauthorized users. In the next step, you will configure your Jitsi Meet instance to only allow registered users to create conference rooms.
Step 5 — Locking Conference Creation
In this step, you will configure your Jitsi Meet server to only allow registered users to create conference rooms. The files that you will edit were generated by the installer and are configured with your domain name.
The variable your_domain will be used in place of a domain name in the following examples.
First, open /etc/prosody/conf.avail/your_domain.cfg.lua with a text editor:
- sudo nano /etc/prosody/conf.avail/your_domain.cfg.lua
Edit this line:
...
authentication = "anonymous"
...
To the following:
...
authentication = "internal_plain"
...
This configuration tells Jitsi Meet to force username and password authentication before allowing conference room creation by a new visitor.
Then, in the same file, add the following section to the end of the file:
...
VirtualHost "guest.your_domain"
authentication = "anonymous"
c2s_require_encryption = false
This configuration allows anonymous users to join conference rooms that were created by an authenticated user. However, the guest must have a unique address and an optional password for the room to enter it.
Here, you added guest. to the front of your domain name. For example, for jitsi.your-domain you would put guest.jitsi.your-domain. The guest. hostname is only used internally by Jitsi Meet. You will never enter it into a browser or need to create a DNS record for it.
Open another configuration file at /etc/jitsi/meet/your_domain-config.js with a text editor:
- sudo nano /etc/jitsi/meet/your_domain-config.js
Edit this line:
...
// anonymousdomain: 'guest.example.com',
...
To the following:
...
anonymousdomain: 'guest.your_domain',
...
Again, by using the guest.your_domain hostname that you used earlier this configuration tells Jitsi Meet what internal hostname to use for the un-authenticated guests.
Next, open /etc/jitsi/jicofo/sip-communicator.properties:
- sudo nano /etc/jitsi/jicofo/sip-communicator.properties
And add the following line to complete the configuration changes:
org.jitsi.jicofo.auth.URL=XMPP:your_domain
This configuration points one of the Jitsi Meet processes to the local server that performs the user authentication that is now required.
Your Jitsi Meet instance is now configured so that only registered users can create conference rooms. After a conference room is created, anyone can join it without needing to be a registered user. All they will need is the unique conference room address and an optional password set by the room’s creator.
Now that Jitsi Meet is configured to require authenticated users for room creation you need to register these users and their passwords. You will use the prosodyctl utility to do this.
Run the following command to add a user to your server:
- sudo prosodyctl register user your_domain password
The user that you add here is not a system user. They will only be able to create a conference room and are not able to log in to your server via SSH.
Finally, restart the Jitsi Meet and Nginx processes to load the new configuration:
- sudo systemctl restart prosody.service
- sudo systemctl restart jicofo.service
- sudo systemctl restart jitsi-videobridge2.service
- sudo systemctl restart nginx
The Jitsi Meet instance will now request a username and password with a dialog box when a conference room is created.

Your Jitsi Meet server is now set up and securely configured.
Conclusion
In this article, you deployed a Jitsi Meet server that you can use to host secure and private video conference rooms. You can extend your Jitsi Meet instance with instructions from the Jitsi Meet Wiki.
Thanks for learning with the DigitalOcean Community. Check out our offerings for compute, storage, networking, and managed databases.
About the author(s)
I have been a Linux Systems Administrator and technical content creator for more than 20 years. I am passionate about using and promoting OSS.
Former Senior Technical Editor at DigitalOcean, with a strong focus on DevOps and System Administration content. Areas of expertise include Terraform, PyTorch, Python, and Django.
Still looking for an answer?
This textbox defaults to using Markdown to format your answer.
You can type !ref in this text area to quickly search our full set of tutorials, documentation & marketplace offerings and insert the link!
sudo /usr/share/jitsi-meet/scripts/install-letsencrypt-cert.sh
This script will:
- Need a working DNS record pointing to this machine(for domain jitsi.anand2.aynvideoconf.ml)
- Download certbot-auto from https://dl.eff.org to /usr/local/sbin
- Install additional dependencies in order to request Let’s Encrypt certificate
- If running with jetty serving web content, will stop Jitsi Videobridge
- Configure and reload nginx or apache2, whichever is used
- Configure the coturn server to use Let’s Encrypt certificate and add required deploy hooks
- Add command in weekly cron job to renew certificates regularly
You need to agree to the ACME server’s Subscriber Agreement (https://letsencrypt.org/documents/LE-SA-v1.1.1-August-1-2016.pdf) by providing an email address for important account notifications Enter your email and press [ENTER]: anand.dadhich@ayninfotech.com Saving debug log to /var/log/letsencrypt/letsencrypt.log Plugins selected: Authenticator webroot, Installer None Obtaining a new certificate Performing the following challenges: http-01 challenge for jitsi.anand2.aynvideoconf.ml Using the webroot path /usr/share/jitsi-meet for all unmatched domains. Waiting for verification… Challenge failed for domain jitsi.anand2.aynvideoconf.ml http-01 challenge for jitsi.anand2.aynvideoconf.ml Cleaning up challenges Some challenges have failed.
IMPORTANT NOTES:
-
The following errors were reported by the server:
Domain: jitsi.anand2.aynvideoconf.ml Type: dns Detail: DNS problem: NXDOMAIN looking up A for jitsi.anand2.aynvideoconf.ml - check that a DNS record exists for this domain
I am Facing this issue! Will you please help me in solving this problem
cat /usr/share/jitsi-meet/your_domain/accounts/*.dat !! Shows the passwords for all accounts unencrypted, in CLEAR TEXT !! prosody saves unencrypted passwords, that is VERY UNSAFE and DANGEROUS
- Table of contents
- Prerequisites
- Step 1 — Setting the System Hostname
- Step 2 — Configuring the Firewall
- Step 3 — Installing Jitsi Meet
- Step 4 — Obtaining a Signed TLS Certificate
- Step 5 — Locking Conference Creation
- Conclusion
Deploy on DigitalOcean
Click below to sign up for DigitalOcean's virtual machines, Databases, and AIML products.
Become a contributor for community
Get paid to write technical tutorials and select a tech-focused charity to receive a matching donation.
DigitalOcean Documentation
Full documentation for every DigitalOcean product.
Resources for startups and SMBs
The Wave has everything you need to know about building a business, from raising funding to marketing your product.
Get our newsletter
Stay up to date by signing up for DigitalOcean’s Infrastructure as a Newsletter.
New accounts only. By submitting your email you agree to our Privacy Policy
The developer cloud
Scale up as you grow — whether you're running one virtual machine or ten thousand.
Get started for free
Sign up and get $200 in credit for your first 60 days with DigitalOcean.*
*This promotional offer applies to new accounts only.
